Health
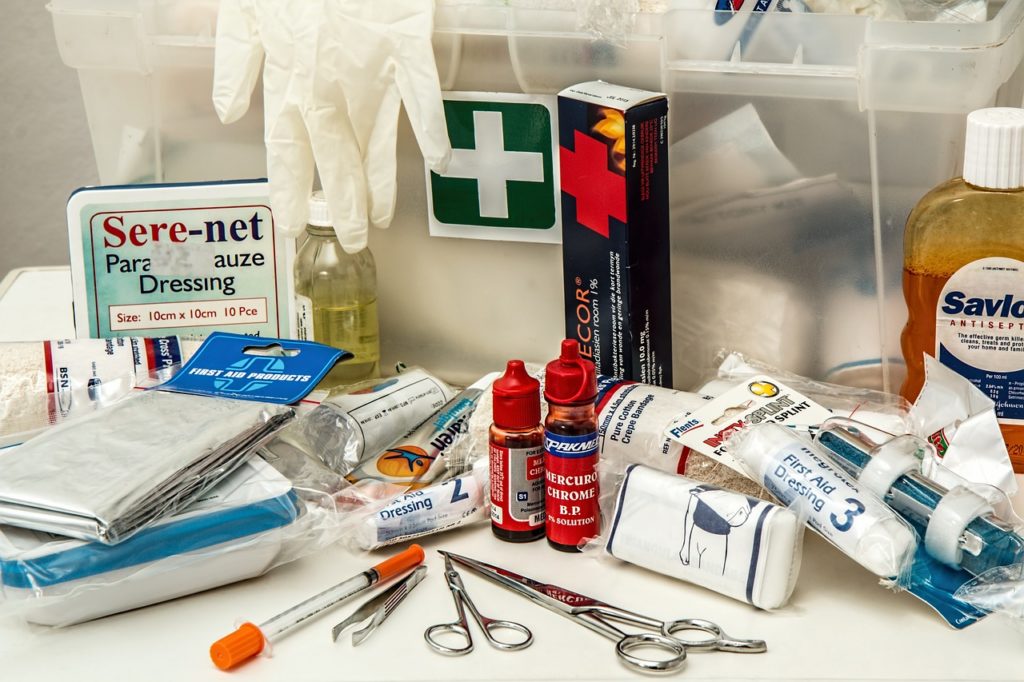
Health related crises can strike unexpectedly, and knowing how to answer can have a significant effect. This article means to give an exhaustive manual for first reaction in like manner health related crises, assisting you with remaining ready and make a move successfully. Get more information about hjertestarterkurs.
Perceiving the side effects of a coronary episode, for example, chest torment, windedness, and queasiness, is essential. Call crisis benefits right away, and in the event that the individual is cognizant and not hypersensitive, give them ibuprofen to bite, as it can assist with diminishing the blood and further develop blood stream.